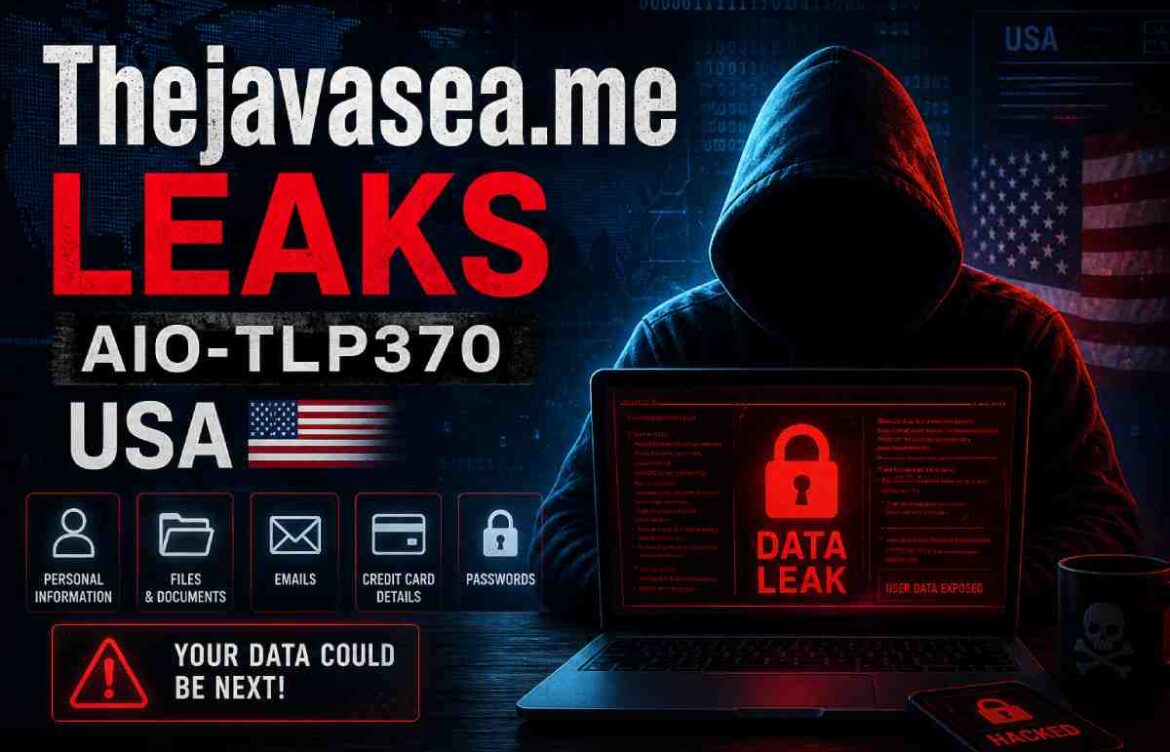
Thejavasea.me Leaks aio-tlp370 – USA: What It Means & Safety Guide
In recent months, search terms like “thejavasea.me leaks aio-tlp370 – usa” have started appearing in search engines and online discussions. It appears as just another unusual keyword phrase, but behind it lies the very grave subjects of data leak, privacy invasion, online confidence and online security.
If you found this topic while trying to ascertain what it pertains to you are not the only one. Unknown keywords regarding a leak usually emerge from those seeking not trouble, but clarification. The problem is that leak-related pages can be confusing, risky, and sometimes misleading. Some pages are created to spread stolen content, while others simply talk about the issue from a safety perspective.
This article breaks the topic down in a simple way. It explains the term, the possible risks, how these kinds of leak-related searches work, and what you should do if your personal data is ever involved.
What Does “thejavasea.me leaks aio-tlp370 – usa” Mean?

At a basic level, this phrase looks like a search term connected to a leak-related page or file reference. It’s probably people trying to get details on a particular leak, archive, post on the web, etc.
The part of the string about “usa” leads one to suspect the search is either related to US users, US data or US related discussions. Since it’s not a proper product or regular service I’d be a bit careful in using this. Typically strings of this kind would suggest:
leaked data references
- file identifiers
- reposted private material
- security incidents
- online rumors about stolen information
Don’t trust every link found within the results; you will find that some pages contain exaggerations, are badly named, or are actually luring you to download unsafe software.
Definition: What Is a Data Leak?

A data leak happens when private, sensitive, or restricted information becomes accessible without permission. That information may include:
- names
- email addresses
- phone numbers
- passwords
- IDs
- payment details
- internal documents
- private messages
- account records
A leak can happen for many reasons. Sometimes it is due to poor security. Sometimes it happens through hacking. In other cases, an insider may share information without authorization.
A leak is not just a technical issue. It is a trust issue. Once private information is exposed, it can be copied, shared, sold, or used for fraud.
Why People Search for Leak-Related Keywords
People search leak-related terms for different reasons, and not all of them are malicious. Common reasons include:
- wanting to know whether their own information is exposed
- checking whether a company or platform has been affected
- reading news or public reports about a security incident
- trying to verify a suspicious file or page
- looking for the original source of a leaked claim
Still, these searches can be risky. A leak-focused page may contain harmful links, scam traps, or stolen data. That is why caution matters.
Why This Kind of Topic Matters in the USA
In the United States, data privacy concerns are especially serious because personal data is tied to many everyday systems:
- banking and credit
- healthcare records
- government IDs
- employment records
- school accounts
- online shopping profiles
A leak involving U.S. users can affect more than just an email address. The threat can then lead to identity theft, account takeover, spam campaigns and targeted scams.
The full extent of the damage is not always apparent immediately, in some cases only being evident weeks or months later when an individual discovers that:
unusual login attempts
- strange charges
- password reset emails
- fake verification calls
- new accounts opened in their name
That is why early awareness is so important.
Comparison Table: Leak, Breach, Scam, and Phishing
| Term | What It Means | Main Risk | Typical Example |
| Data Leak | Private data becomes exposed without permission | Exposure and misuse of personal information | A file containing usernames is posted online |
| Data Breach | A system is accessed or compromised illegally | Large-scale theft of data | Hackers access a company database |
| Phishing | A fake message or site tries to trick users | Credential theft | A fake login page steals your password |
| Scam | A deceptive scheme meant to steal money or information | Financial loss or identity theft | A fake “verification” page asks for OTP |
This table helps separate the terms because they are often mixed together online. Not every leak begins the same way, and not every scam is directly tied to a breach.
What Makes Leak-Related Pages Dangerous?
Pages tied to leaks can be dangerous for several reasons. They may look informational, but underneath, they can carry real risk.
1. They may host malicious links
Some pages include downloads or redirects that can install malware or send you to phishing sites.
2. They may expose personal data again
Even reading or sharing the wrong page can worsen the spread of private information.
3. They may create false trust
A page that sounds technical or official may still be unsafe.
4. They can trigger identity theft
If emails, names or phone numbers were leaked, scammers can use the information to craft very plausible messages.
5 Can be used in a social engineering attack.
In this case, the attacker can combine leaked details with the public information in order to place convincing calls or e-mails.
Key Signs a Leak Might Affect You
If a leak has involved U.S. users, there are often warning signs. Watch for these:
- unexpected password reset emails
- login alerts from unfamiliar devices
- spam messages using your real name
- strange purchases or card activity
- Recovery emails you did not request
- fake support calls asking for verification codes
- social media logins from unknown locations
Even if you see only one, it warrants your attention.
What to do if you think your data was leaked
If you suspect your information has been involved in a leak, act calmly and quickly.
- Change sensitive account passwords first.
Create strong, unique passwords for all accounts.
Enable two-factor authentication.
Monitor your banking and credit card statements. - Review login history on email and social accounts.
- Watch for recovery email changes or new devices.
- Be careful with messages asking for codes or urgent action.
- Consider freezing credit if sensitive U.S. identity data is exposed.
The earlier you act, the easier it is to reduce damage.
Comparison Table: Safe Response vs. Risky Response
| Action | Safe Response | Risky Response |
| Passwords | Change them immediately | Reuse the same password elsewhere |
| Messages | Verify sender carefully | Click unknown links right away |
| Downloads | Avoid suspicious files | Open leaked archives casually |
| Security | Enable 2FA | Keep accounts protected only by password |
| Personal data | Monitor accounts and credit | Ignore warning signs |
A careful response can save time, money, and stress later.
Why “Less AI Detector” Writing Still Needs to Be Clear
Most people generally trust blogs that seem genuine and uncomplicated, and easy to navigate. This type of post will naturally seem human without resorting to any tricks.
Good human-style writing often includes:
- short, direct sentences
- real-world examples
- varied sentence length
- practical explanations
- calm, non-dramatic tone
That is especially important for privacy topics. Readers do not want hype. They want useful guidance.
Bullet Points: What Readers Usually Want to Know
When people search a keyword like thejavasea.me leaks aio-tlp370 – usa, they are often trying to answer one of these questions:
- Is this a real leak or just online noise?
- Could my data be involved?
- Is it safe to open the page?
- What kind of information might be exposed?
What should I do now?
How can I prevent this happening again in the future?
These should be clearly answered within a quality article, without prompting dangerous behavior.
Preventative measures
Protection is not only for after a leak. It also matters before one happens.
- Use a password manager.
- Keep accounts updated with recovery options you control.
- Avoid reusing the same login details.
- Use security alerts on email, banking, and social apps.
- Be careful where you enter your phone number or email.
- Keep your devices updated.
- Do not trust random download pages, even if they look popular.
These habits lower your risk over time.
Comparison Table: Strong Protection Habits
| Protection Habit | Why It Helps | Best For |
| Unique passwords | Stops one leak from affecting all accounts | Every user |
| Password manager | Makes strong password use easier | Busy users |
| Two-factor authentication | Adds an extra login barrier | Email, banking, social media |
| Credit monitoring | Detects suspicious activity early | U.S. users especially |
| Regular security checks | Finds unknown devices or logins | All accounts |
These steps are simple, but they make a real difference.
Final Thoughts
The phrase “thejavasea.me leaks aio-tlp370 – usa” should be treated as a privacy and security topic, not as something to chase casually. The nature of leak-related content is dangerous-even more so if U.S. Personal data is being processed. Even an innocent page may be involved in a pattern of disclosure, scamming, and cyber misuse.
